Basic Authentication is being deprecated – Help!?
Last month Microsoft announced that basic authentication is being turned off on October 13, 2020. There are still a lot of admins who are unaware of this change and what effect this will have on their organization. A reader recently asked me what this meant for them and I thought => let’s make a blog post for this!
Update: Because of COVID-19 Microsoft has made some changes to the timeline:
- Deprecation is postponed to second half of 2021
- New tenants will have basic auth disabled by default (through security defaults)
- Beginning October 2020, basic authentication will be disabled in tenants that don’t use it.
What is basic authentication
But what does this mean? What is basic authentication? Basic authentication is the old way for a client to authenticate to a server. During this authentication, the clients sends it’s username and password to the server everytime. Basic Authentication doesn’t support sending the device information that’s needed for some Conditional Access policies nor does it support multifactor authentication. This makes it an insecure way of authenticating. Basic Authentication is often used by attackers to perform password spray attacks.
The alternative for basic (sometimes also referred to as legacy) authentication is modern authentication. Modern Authentication has been enabled by default in Office 365 since 2016 and is the way forward.
What is happening?
First off, it is important to note that Microsoft is only turning of basic auth for Exchange Online. All other workloads (Sharepoint Online, Skype for Business Online, Exchange on-prem) will still have support for basic authentication (however, I recommend to migrate all workloads to modern auth).
So as of now, Microsoft is turning off support for basic authentication for the following protocols:
- Exchange ActiveSync
- POP
- IMAP
- Remote Powershell
- EWS (this was announced in 2018)
Basic Authentication for SMTP Auth is still supported, as Microsoft acknowledges that this is still widely used. It is strongly advised to start migrating these workloads to Modern Authentication too, as this improves security a lot.
POP & IMAP
POP and IMAP are protocols that are widely used by various applications to send and receive mails. Microsoft is planning to add support for modern authentication to these protocols, but no timeline has been announced. I strongly urge you to update your in-house applications to support OAuth 2.0 and contact your third-party vendors.
Desktop Applications
Modern authentication is only supported out of the box for Outlook 2016 and 2019. Outlook 2013 can be configured to support modern authentication, but it requires a few registry edits and an up-to-date client. Outlook 2010 doesn’t support modern authentication at all. So if you currently use Outlook 2010 to connect to Exchange Online, it is recommended to update to Office 365 ProPlus or Office 2019.
Mobile applications
The road to modern authentication on mobile differs between the two platforms. iOS Mail has been supporting modern authentication since iOS 11, so this app can be used in the future.
Android hasn’t been such a good boy however. Gmail and most of the built-in email clients don’t support modern authentication. The ones that do are Nine for Work and the Samsung email client (discovered that one last week. It doesn’t support Android Enterprise).
However I would recommend to migrate all mobile clients to the one that rules them all: Outlook Mobile? Why is that?
- Same experience across Android & iOS (good for your users and suppport staff)
- Support for App Protection Policies
- Support for extra features like: adding shared mailbox, sending your availability, adding Teams meetings and much more!
I suspect Google will catch up and add Modern Authentication to the Gmail app but I still recommend switching to the Outlook app as mentioned above. Users can be hesitant when forced to switch as the experience between the Gmail and Outlook apps are much different. That’s why I recommend to have management buy-in and train your staff to know the benefits of Outlook Mobile.
Update 04/2020: Gmail support modern auth starting from Android 9.0
Remote Powershell
Exchange Online Powershell has supported Modern Authentication for a while now. So that is an easy one 🙂
EWS
End-of-life for EWS basic auth in Exchange Online has been announced in 2018 and this should be common knowledge for now. EWS has support for modern authentication built-in so you don’t have to throw away your EWS just yet. But I do recommend migrating your apps to the Microsoft Graph API as this is the way forward. EWS is not receiving any feature updates and Graph has been positioned as the way forward.
Third Party Tools/Applications
But what if you have third party tools, appliances or applications that use basic authentication to connect to your Exchange Online mailboxes? Here you have two simple options:
- Ask your vendor to support modern auth
- Migrate to an app that supports modern auth
There isn’t much else you can do unfortunately. I was at a customer this week that uses Veeam Backup for Office 365. Veeam already uses modern authentication for some workloads but still depends on basic authentication to get information about your users mailboxes. It’s advised to contact your Veeam rep and ask them about their roadmap.
Dynamics CRM is also one of those apps that doesn’t support modern auth in all versions. The recommended way here is to upgrade to a newer version or Dynamics Online.
Discovering basic authentication
Most organizations know which applications are authenticating to Exchange Online, but there is always some shadow IT going around.
Microsoft is working on a tool to discover basic authentication, but there is no ETA for this one.
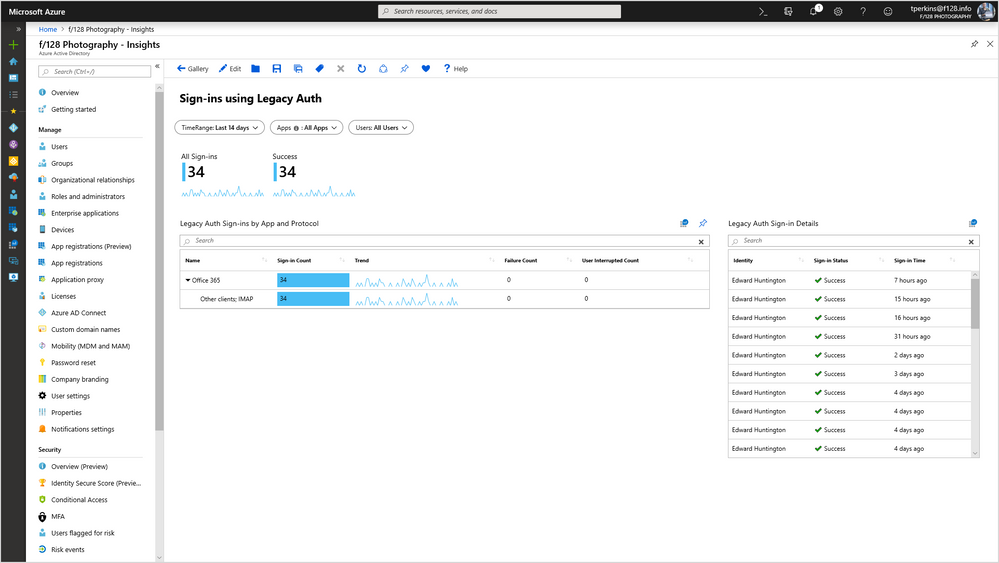
In the mean time, Azure Active Directory Premium users can use the sign-ins monitoring page to filter those users.

If you need some more detailed insights, you can use the Log Analytics Workbook which gives you an easy visual representation of all the legacy protocols which are still running in your environment.
Turning off basic authentication proactively
What if you want to turn off basic authentication before October 13? Well you have two options. The easiest one is to use conditional access, with one policy you can disable basic auth for your whole tenant or a group of users. But it is important to remember that conditional access policies only have affect after the users have authenticated.
Therefore it is also recommended to use authentication policies in Exchange Online, these policies take affect before authentication happens and will protect you from password spray attacks.
Multifactor Authentication
While Microsoft isn’t forcing Multifactor Authentication yet. Please, please enable it for your users. It improves your security drastically and protects your from leaked credentials, phishing attacks, password reuse etcetera.
Turning on MFA can have a big impact on the users, therefore it is recommended to use Conditional Access and reduce the number of MFA prompts a user receives.
For smaller customers that don’t have access to Azure AD Premium licensing, Microsoft has just released security defaults. This enables a few things at once:
- Risk Based Conditional Access for users
- MFA for administrators
- Disabling legacy authentication
- Protecting Azure actions
These security defaults do not support any exclusions and can’t be used in conjunction with Conditional Access. These settings are rumored to be replacing the baseline policies, so I would recommend migrating away from these and adapting the security defaults instead..
Last year I wrote a series about enabling MFA, it is a bit outdated and requires an update but is still pretty up-to-date as of now.
Have any questions or remarks about this blog? Feel free to leave a comment or reach out through social media!
Categories
