Sync Named Locations to MCAS IP Ranges using Azure Automation
Every Microsoft 365 Security engineer has the same struggle: maintaining corporate IP-address range needs to be done in two places. Once in trusted named locations in Azure AD and once in corporate ‘IP ranges’ in MCAS. It is really important to configure these both. In Azure AD, (trusted) named locations are used in Conditional Access policies and in MCAS, the ranges are used within alert policies and can be helpful during investigations.
After my latest blog on saving named locations to Log Analytics, Nicolas DiCola (Program Manager for Microsoft) contacted me if there was a way to sync these two locations. As this is a struggle to maintain indeed, I decided to write up a solution which syncs all your trusted named locations from Azure AD into corporate IP ranges in MCAS. This solution is natively built in Azure Automation and uses a runbook that runs weekly to sync your IP ranges.
The runbook is configured to run weekly (on Monday) and will execute a one way sync, in which all trusted named locations will be copied/updated to corporate IP ranges in MCAS. If any changes are made in named locations, these will be copied to MCAS during the next run. As this is a one way sync, all changes to the IP ranges should be done in named locations. This solution will delete any trusted IP address ranges in MCAS that aren’t present in trusted named locations.
The script uses some undocumented MCAS API endpoints, so I cannot guarantee these endpoint will kept the same. But I do vow to keep this project alive and update it as much as possible.
Using the buttons below, you can deploy the ARM Template from Github directly into your Azure account.


The ARM template will deploy the following resources:
- Azure Automation account
- 1 Azure Runbook (contents can be found here)
- 1 schedule (by default: weekly on Monday)
Before deploying, you will need to do a few preparations:
- Create an Azure AD Application with Policy.Read.All application permissions. Generate an application secret and copy the secret, application ID and tenant ID
- Generate a MCAS API key and copy it together with the MCAS API URL.
When deploying the ARM template, you will need to fill in 5 parameters:
- AutomationAccount: Name of the Azure automation account that will be deployed
- credentials_GraphAPI_clientid: Application ID for the Azure AD Application
- credentials_GraphAPI_password: Application Secret for the Azure AD Application
- credentials_MCAS_URL: MCAS API URL in the format: “365bythijs.eu2.portal.cloudappsecurity.com”
- credentials_MCAS_APIKEY: MCAS API key
- Tenant ID: Tenant ID for the application
After you deploy this solution, it will run on the first Monday. If you want, you can force a sync by opening the Automation account, selecting Runbooks and then select the ‘SyncNamedLocationsToMCAS’ runbook. With the runbook open, click ‘Start’.


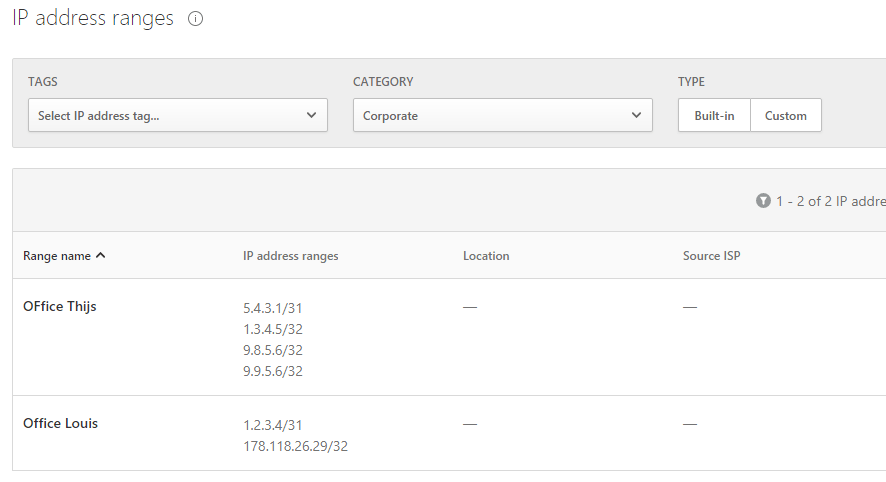
After the script has run, you will see all your trusted named locations copied into IP address ranges in MCAS with the category ‘Corporate’
I also created a local version of this script which enables you to run it locally as a test or perform a one way copy (for example when you are setting up a new tenant).
I hope you have as much with this as I had with creating this solution Do me in the loop of your experience, if you have any ideas/improvements for a v2, do get in touch with me!
Categories
